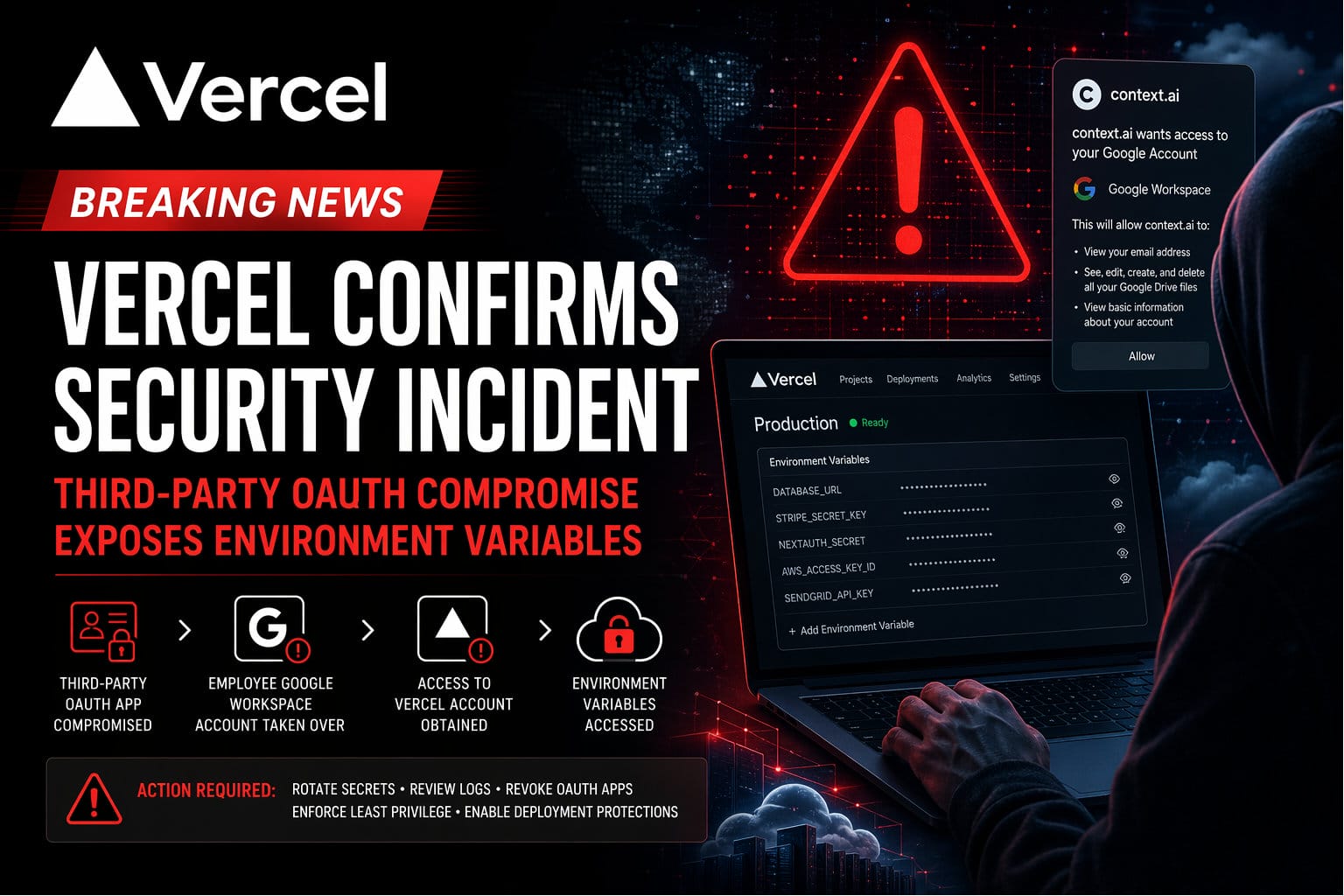
In a development that underscores the fragility of modern SaaS ecosystems, Vercel has confirmed a security incident originating not within its own infrastructure, but through a compromised third-party integration.
What Is Vercel—and Why This Matters
For readers less familiar, Vercel is a cloud platform built for frontend developers, best known for powering fast, globally distributed web applications. It provides hosting, serverless functions, edge computing, and deployment automation—often with a single command from a developer’s terminal.
It is also the company behind Next.js, one of the most widely used React frameworks for building modern web applications. Organizations ranging from startups to large enterprises rely on Vercel to deploy production systems, manage environments, and store critical configuration data such as API keys and service credentials.
In practical terms, Vercel sits directly in the application delivery pipeline. That positioning makes it both operationally powerful—and an attractive target.
How the Breach Occurred
According to Vercel’s official bulletin, the breach began with the compromise of a Context.ai OAuth application connected to an employee’s Google Workspace account. That foothold allowed the attacker to escalate access—first into the employee’s identity layer, then into their Vercel account, and ultimately into a subset of customer environments.
Once inside, the attacker was able to enumerate and decrypt certain environment variables classified as “non-sensitive.” While Vercel maintains that sensitive variables were protected under stricter controls, the incident highlights a critical reality: once an attacker achieves legitimate application-layer access, traditional safeguards like encryption at rest provide limited resistance.
What Was Accessed—and What Was Not
Vercel has stated:
- A limited number of customer accounts were affected
- Non-sensitive environment variables may have been exposed
- No evidence suggests compromise of npm packages or broader supply chain tampering
- Additional impacted accounts were identified after deeper log analysis
This distinction matters. The breach does not appear to be systemic across all customers, nor does it indicate platform-wide compromise. However, for affected users, any exposed environment variable—regardless of classification—should be treated as compromised.
The Real Issue: Governance, Not Just Security
This incident is not fundamentally about encryption, firewalls, or even zero-day exploits. It is about governance breakdown across interconnected systems.
The attack path raises immediate questions:
- Was there a controlled inventory of authorized OAuth applications?
- Were high-risk scopes restricted or monitored in Google Workspace?
- Did identity-based access controls enforce boundaries between employee accounts and production environments?
- Were environment variables consistently classified and enforced by policy?
These are not tactical failures. They are governance failures—specifically in third-party risk management and identity control.
Detection and Response
Vercel has indicated that log telemetry played a central role in identifying and assessing the breach. Their investigation included reviewing:
- Requests to the Vercel network
- Environment variable access events
- Deployment and account activity logs
Post-incident, the company has introduced:
- Improved activity logging visibility
- Enhanced safeguards around environment variables
- Stronger default security configurations
These changes suggest that observability and policy enforcement were areas of immediate focus following the incident.
Immediate Actions for Vercel Users
If your organization uses Vercel, the response should be decisive and immediate:
- Rotate all environment variables, especially those not explicitly marked as sensitive
- Audit activity logs for unusual access patterns or deployments
- Revoke unknown or unused OAuth applications across identity providers
- Enable stronger deployment protections and access controls
- Revalidate least-privilege access across teams and environments
- Assess downstream exposure from any potentially compromised credentials
Strategic Takeaway
This incident reinforces a broader shift in cybersecurity risk:
The perimeter is no longer your infrastructure.
It is your identity layer—and every integration connected to it.
Third-party tools, particularly those leveraging OAuth, now represent a primary attack vector. The convenience they offer is matched by the implicit trust they inherit.
Organizations that treat integrations as extensions of their security boundary—rather than external conveniences—will be better positioned to withstand this class of attack.
The rest will continue to learn the same lesson, one incident at a time.
