Cybersecurity governance is often assessed as a collection of activities—risk assessments, policies, controls, and reports. But under scrutiny, those activities are not evaluated in isolation.
They are evaluated as a system.
A system that either produces a coherent evidentiary record… or does not.
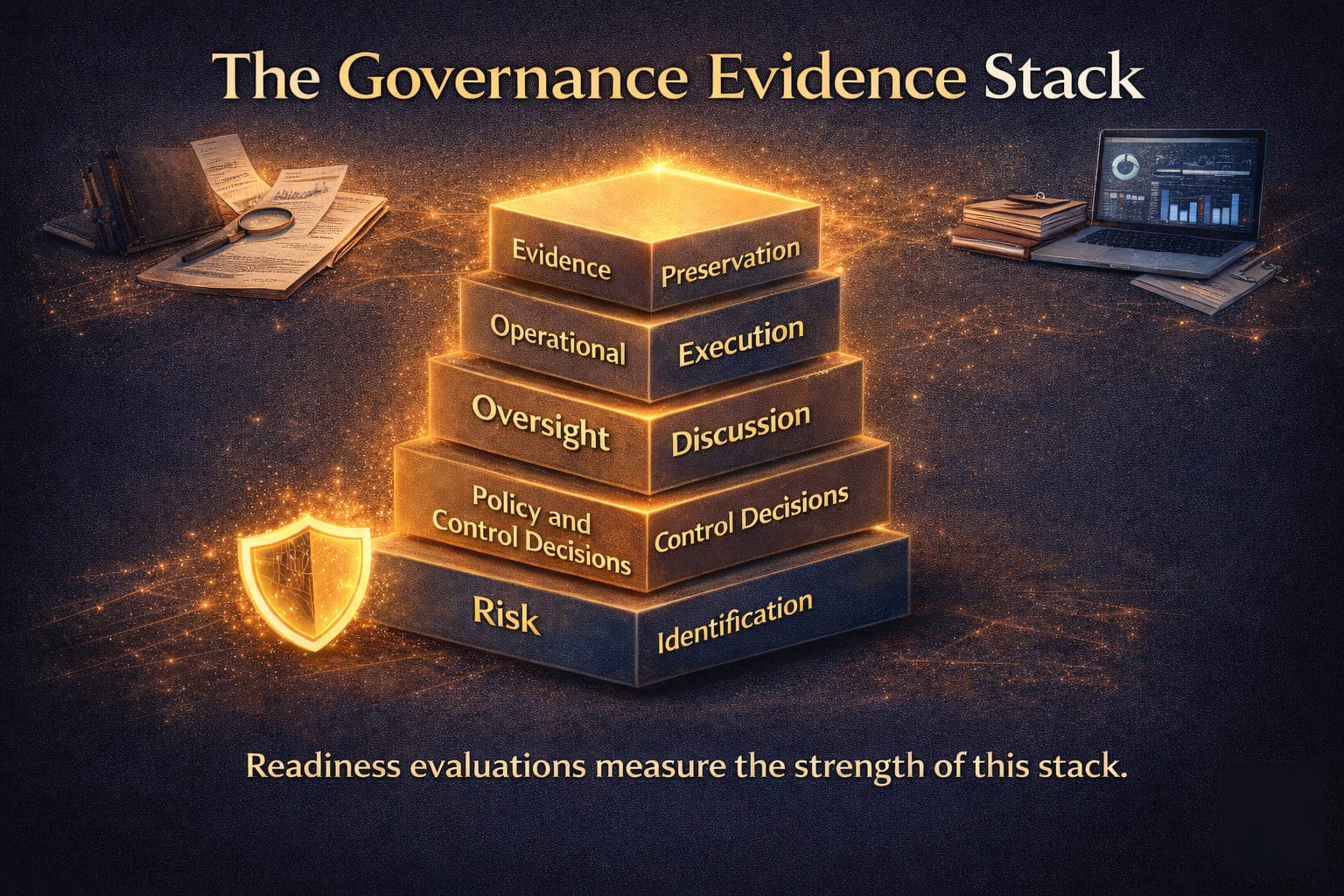
This is the Governance Evidence Stack.
It defines how organizations transform cybersecurity governance from fragmented effort into defensible proof of oversight. When this stack is complete, leadership can demonstrate that risk was identified, decisions were made, oversight was exercised, execution occurred, and evidence was preserved.
When it is incomplete, gaps emerge—not in activity, but in proof.
Layer 1: Risk Identification
Every evidentiary structure begins with risk.
Organizations must be able to demonstrate:
- What risks were identified
- How those risks were assessed
- How they were prioritized
- How they were communicated to leadership
Risk identification is not simply a technical inventory. It is the foundation of governance awareness.
If risks were not clearly defined in decision-relevant terms, every downstream layer weakens. Leadership cannot oversee what was never clearly articulated.
Evidence at this layer includes:
- Risk registers
- Threat assessments
- Scenario analyses
- Materiality determinations
Without this layer, there is no starting point for defensible oversight.
Layer 2: Policy and Control Decisions
Once risks are identified, organizations must demonstrate how they chose to respond.
This is where governance translates awareness into intent.
Leadership must be able to show:
- What policies were established
- What controls were selected or approved
- Why those decisions were made
- How those decisions align to risk
Policies and controls are not evidence of execution. They are evidence of decision-making.
This distinction matters.
An organization may have extensive controls in place, but if it cannot demonstrate how and why those controls were chosen, governance appears reactive rather than deliberate.
Evidence at this layer includes:
- Policy documents and approvals
- Control frameworks and mappings
- Risk acceptance or mitigation decisions
- Board or committee approvals
This layer establishes that leadership engaged with risk in a structured and intentional way.
Layer 3: Oversight Discussion
Governance is not a one-time decision. It is an ongoing discipline of review, challenge, and adjustment.
Oversight discussion is where leadership demonstrates active engagement.
The critical question is not whether meetings occurred, but whether meaningful governance took place.
Organizations must be able to show:
- What was discussed
- What questions were raised
- What challenges were made
- What follow-up actions were required
This is often the most overlooked layer—and the most revealing.
Minutes that reflect passive acceptance weaken governance.
Minutes that reflect informed questioning strengthen it.
Evidence at this layer includes:
- Board and committee minutes
- Risk review discussions
- Escalation records
- Decision logs
This layer transforms governance from structure into observable behavior.
Layer 4: Operational Execution
Governance decisions must translate into action.
Operational execution demonstrates that policies and controls were not only defined, but implemented and functioning.
However, execution alone is not sufficient. It must be tied back to governance intent.
Organizations must demonstrate:
- That controls were implemented as designed
- That processes were followed consistently
- That monitoring and validation occurred
- That deviations were identified and addressed
Execution without traceability appears disconnected.
Execution aligned to governance decisions becomes evidence.
Artifacts at this layer include:
- Control implementation records
- System configurations
- Access reviews and logs
- Monitoring and alerting outputs
This layer answers the question: Did the organization do what it said it would do?
Layer 5: Evidence Preservation
The final layer determines whether any of the above can be proven.
Evidence that is not preserved is indistinguishable from evidence that never existed.
Organizations must ensure that governance artifacts are:
- retained in a structured and accessible manner
- protected from alteration or loss
- time-bound and version-controlled
- retrievable under scrutiny
This is not a technical storage problem. It is a governance requirement.
If evidence cannot be produced when needed, the entire stack collapses.
Artifacts at this layer include:
- archived reports and records
- audit trails and logs
- version histories
- retention policies
This layer ensures that governance survives beyond the moment it occurred.
Evaluating the Stack
Cybersecurity readiness is often measured through maturity models, control frameworks, and compliance checklists.
But under real scrutiny, readiness is evaluated differently.
It is measured by the strength of the Governance Evidence Stack.
- Are risks clearly identified and documented?
- Are decisions traceable to those risks?
- Is oversight observable in governance discussions?
- Is execution aligned with decisions?
- Is evidence preserved and retrievable?
Weakness in any layer introduces doubt.
Strong alignment across all five layers produces defensibility.
From Activity to Structure
The Governance Evidence Stack reframes cybersecurity governance as an integrated system of proof.
It shifts the focus:
From isolated activities → to connected evidence
From implementation → to traceability
From reporting → to defensibility
This model does not require perfection.
It requires coherence.
Because in the end, governance is not evaluated by what was done in isolation.
It is evaluated by whether the full story can be reconstructed—clearly, consistently, and credibly.
And that story is only as strong as the stack that supports it.