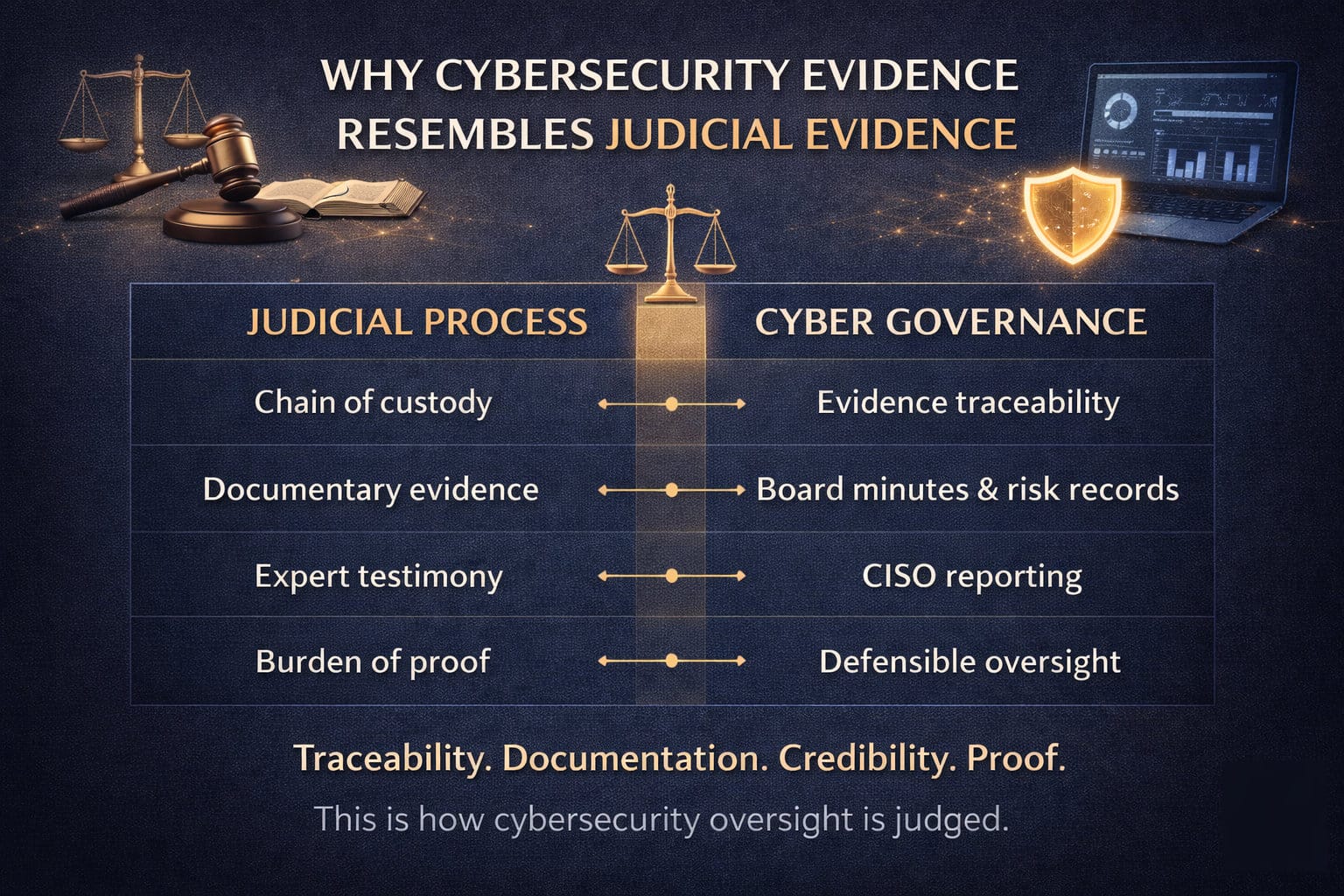
Cybersecurity governance is increasingly evaluated in environments that look less like technical reviews and more like legal proceedings.
After a material incident, organizations are not simply asked what happened. They are asked to explain, substantiate, and defend their actions. The standard shifts from operational performance to evidentiary credibility.
This is why cybersecurity evidence closely resembles judicial evidence.
The analogy is not rhetorical. It is structural.
Courts, regulators, insurers, and investigators assess organizations using principles that mirror the legal system: traceability, documentation, credibility of sources, and burden of proof. Governance that fails to meet these standards is often judged as inadequate—regardless of the technical sophistication of controls.
To understand this shift, it is useful to examine how core elements of judicial evidence map directly to cybersecurity governance.
Chain of Custody → Evidence Traceability
In legal proceedings, chain of custody establishes that evidence has been handled in a controlled, documented manner from origin to presentation. If that chain is broken, the evidence may be deemed unreliable or inadmissible.
In cybersecurity governance, the equivalent is evidence traceability.
Boards and executives must be able to demonstrate how information about risk moved through the organization:
- When was the risk identified?
- How was it documented?
- Who reviewed it?
- What decisions were made, and when?
If this chain cannot be reconstructed, governance appears fragmented—even if actions were taken. Without traceability, oversight cannot be proven.
Documentary Evidence → Board Minutes and Risk Records
In court, documentary evidence—contracts, communications, records—forms the backbone of most cases. It provides a persistent, reviewable account of events and decisions.
In cyber governance, documentary evidence takes the form of:
- Board and committee minutes
- Risk registers and assessments
- Policy approvals and revisions
- Assurance reports and findings
These artifacts are not administrative formalities. They are the record of governance intent and action. When they are incomplete, inconsistent, or absent, organizations lose their ability to demonstrate that oversight occurred in a disciplined and informed manner.
Expert Testimony → CISO and Leadership Reporting
Legal proceedings often rely on expert witnesses to interpret complex subjects and provide informed opinion.
In cybersecurity governance, this role is fulfilled by the Chief Information Security Officer and other subject matter experts.
However, credibility depends on more than expertise. It depends on:
- independence of reporting
- clarity of communication
- consistency over time
- alignment with documented records
If expert reporting is vague, overly technical, or disconnected from governance artifacts, it weakens the evidentiary position. Strong governance ensures that expert input is translated into decision-relevant information that can be understood, challenged, and documented.
Burden of Proof → Defensible Oversight
Perhaps the most important parallel is the burden of proof.
In legal contexts, the party under scrutiny must demonstrate that actions were reasonable, appropriate, and supported by evidence. Assertions without substantiation carry little weight.
The same is increasingly true in cybersecurity governance.
Organizations are not expected to eliminate all risk. They are expected to demonstrate that:
- risks were identified and understood
- oversight structures were in place
- decisions were informed and deliberate
- governance processes functioned as intended
This is defensible oversight.
It does not require perfection. It requires proof.
The Implication for Boards and Leadership
This judicial analogy reframes cybersecurity governance in a way that many organizations have not fully internalized.
Governance is not evaluated in real time.
It is evaluated after the fact.
And after the fact, perception is shaped by evidence.
An organization may believe it exercised strong oversight.
But if it cannot produce clear, consistent, and traceable evidence, that belief carries little weight under scrutiny.
Conversely, organizations that maintain disciplined governance records—structured reporting, documented decisions, validated controls—are able to demonstrate reasonableness even in the presence of failure.
This is the difference between assertion and credibility.
From Governance Activity to Evidentiary Discipline
Understanding cybersecurity governance through a judicial lens leads to a critical conclusion:
Governance must be designed with evidence in mind.
This means:
- ensuring that risk discussions are documented in decision-relevant terms
- maintaining traceability of information flow and escalation
- structuring reporting so that expert input becomes part of the evidentiary record
- preserving artifacts that demonstrate oversight over time
These practices do not slow governance. They strengthen it.
They create a system in which leadership actions are not only taken, but provable.
Establishing Intellectual Credibility
The purpose of this analogy is not to suggest that cybersecurity governance is a legal proceeding.
It is to recognize that it is evaluated using similar standards.
Traceability. Documentation. Credibility. Proof.
These are not optional attributes. They are the basis on which oversight is judged.
As the Cyber Evidence Series progresses, this judicial framing will serve as a foundation for understanding how governance artifacts are created, maintained, and evaluated.
Because in the end, cybersecurity governance is not only about managing risk.
It is about being able to prove that it was managed responsibly.